Which Of The Following Scenarios Illustrates A Drive-By Download? UPDATED
Which Of The Following Scenarios Illustrates A Drive-By Download?
Although the terms security threat, security event and security incident are related, in the world of cybersecurity these information security threats have unlike meanings.
A security threat is a malicious act that aims to decadent or steal data or disrupt an organization'due south systems or the entire organization. A security upshot refers to an occurrence during which company data or its network may have been exposed. And an event that results in a data or network breach is called a security incident.
As cybersecurity threats continue to evolve and go more than sophisticated, enterprise It must remain vigilant when it comes to protecting their data and networks. To do that, they first have to understand the types of security threats they're upwards against.
Below are the elevation 10 types of information security threats that Information technology teams need to know nearly.
1. Insider threats
An insider threat occurs when individuals close to an organization who have authorized access to its network intentionally or unintentionally misuse that access to negatively touch the organization's disquisitional data or systems.
Devil-may-care employees who don't comply with their organizations' business rules and policies crusade insider threats. For case, they may inadvertently email customer data to external parties, click on phishing links in emails or share their login information with others. Contractors, business partners and 3rd-political party vendors are the source of other insider threats.
Some insiders intentionally bypass security measures out of convenience or ill-considered attempts to become more productive. Malicious insiders intentionally elude cybersecurity protocols to delete data, steal data to sell or exploit afterwards, disrupt operations or otherwise harm the business.
Preventing insider threats
The list of things organizations tin do to minimize the risks associated with insider threats include the following:
- limit employees' access to just the specific resources they need to do their jobs;
- train new employees and contractors on security awareness earlier allowing them to access the network. Incorporate information nigh unintentional and malicious insider threat awareness into regular security training;
- ready upwards contractors and other freelancers with temporary accounts that expire on specific dates, such as the dates their contracts cease;
- implement two-factor authentication, which requires each user to provide a second piece of identifying information in improver to a password; and
- install employee monitoring software to help reduce the gamble of information breaches and the theft of intellectual property past identifying careless, disgruntled or malicious insiders.
ii. Viruses and worms
Viruses and worms are malicious software programs (malware) aimed at destroying an organisation'due south systems, information and network. A estimator virus is a malicious lawmaking that replicates by copying itself to another program, organisation or host file. It remains fallow until someone knowingly or inadvertently activates it, spreading the infection without the knowledge or permission of a user or organization assistants.
A computer worm is a self-replicating plan that doesn't accept to copy itself to a host program or require human interaction to spread. Its main function is to infect other computers while remaining agile on the infected system. Worms often spread using parts of an operating organization that are automated and invisible to the user. In one case a worm enters a system, it immediately starts replicating itself, infecting computers and networks that aren't fairly protected.
Preventing viruses and worms
To reduce the gamble of these types of information security threats acquired by viruses or worms, companies should install antivirus and antimalware software on all their systems and networked devices and go on that software up to date. In addition, organizations must train users non to download attachments or click on links in emails from unknown senders and to avert downloading free software from untrusted websites. Users should also be very cautious when they utilise P2P file sharing services and they shouldn't click on ads, particularly ads from unfamiliar brands and websites.
3. Botnets
A botnet is a collection of Net-connected devices, including PCs, mobile devices, servers and IoT devices that are infected and remotely controlled by a common blazon of malware. Typically, the botnet malware searches for vulnerable devices beyond the net. The goal of the threat actor creating a botnet is to infect as many connected devices every bit possible, using the computing power and resources of those devices for automated tasks that generally remain hidden to the users of the devices. The threat actors -- ofttimes cybercriminals -- that control these botnets utilise them to send email spam, engage in click fraud campaigns and generate malicious traffic for distributed denial-of-service attacks.

Preventing botnets
Organizations have several ways to forbid botnet infections:
- monitor network operation and activity to detect any irregular network behavior;
- continue the operating system up to date;
- keep all software up-to-date and install whatsoever necessary security patches;
- educate users not to engage in any activeness that puts them at risk of bot infections or other malware, including opening emails or messages, downloading attachments or clicking links from unfamiliar sources; and
- implement antibotnet tools that find and cake bot viruses. In addition, most firewalls and antivirus software include basic tools to notice, forbid and remove botnets.
4. Drive-by download attacks
In a bulldoze-by download attack, malicious code is downloaded from a website via a browser, application or integrated operating arrangement without a user's permission or knowledge. A user doesn't have to click on anything to activate the download. Just accessing or browsing a website can start a download. Cybercriminals can apply drive-by downloads to inject banking Trojans, steal and collect personal information besides as introduce exploit kits or other malware to endpoints.
Preventing drive-past download attacks
One of the all-time means a company tin can forbid drive-by download attacks is to regularly update and patch systems with the latest versions of software, applications, browsers, and operating systems. Users should likewise be warned to stay abroad from insecure websites. Installing security software that actively scans websites can help protect endpoints from bulldoze-by downloads.
5. Phishing attacks
Phishing attacks are a type of information security threat that employs social engineering to trick users into breaking normal security practices and giving upwards confidential data, including names, addresses, login credentials, Social Security numbers, credit card information and other financial information. In most cases, hackers send out fake emails that look as if they're coming from legitimate sources, such as financial institutions, eBay, PayPal -- and even friends and colleagues.
In phishing attacks, hackers attempt to get users to take some recommended action, such as clicking on links in emails that accept them to fraudulent websites that inquire for personal information or install malware on their devices. Opening attachments in emails tin also install malware on users' devices that are designed to harvest sensitive information, send out emails to their contacts or provide remote access to their devices.
Preventing phishing attacks
Enterprises should railroad train users not to download attachments or click on links in emails from unknown senders and avoid downloading free software from untrusted websites.
6. Distributed denial-of-service (DDoS) attacks
In a distributed denial-of-service (DDoS) attack, multiple compromised machines attack a target, such equally a server, website or other network resource, making the target totally inoperable. The flood of connectedness requests, incoming messages or malformed packets forces the target system to slow downwards or to crash and shut downwards, denying service to legitimate users or systems.
Preventing DDoS attacks
To help prevent DDoS attacks, companies should take these steps:
- Implement technology to monitor networks visually and know how much bandwidth a site uses on average. DDoS attacks offer visual clues and so administrators who understand the normal behaviors of their networks will exist improve able to catch these attacks.
- Ensure servers have the capacity to handle heavy traffic spikes and the necessary mitigation tools necessary to address security bug.
- Update and patch firewalls and network security programs.
- Set up protocols outlining the steps to take in the result of a DDoS attack occurring.
7. Ransomware
In a ransomware attack, the victim'due south computer is locked, typically by encryption, which keeps the victim from using the device or information that'due south stored on it. To regain access to the device or information, the victim has to pay the hacker a ransom, typically in a virtual currency such as Bitcoin. Ransomware can exist spread via malicious e-mail attachments, infected software apps, infected external storage devices and compromised websites.
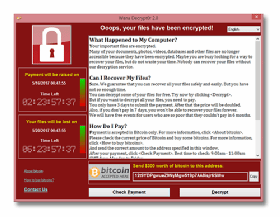
Preventing ransomware
To protect against ransomware attacks, users should regularly support their computing devices and update all software, including antivirus software. Users should avoid clicking on links in emails or opening e-mail attachments from unknown sources. Victims should do everything possible to avoid paying ransom. Organizations should too couple a traditional firewall that blocks unauthorized admission to computers or networks with a program that filters spider web content and focuses on sites that may introduce malware. In add-on, limit the data a cybercriminal tin admission past segregating the network into singled-out zones, each of which requires different credentials.
8. Exploit kits
An exploit kit is a programming tool that enables a person without whatsoever experience writing software code to create, customize and distribute malware. Exploit kits are known by a variety of names, including infection kit, crimeware kit, DIY assault kit and malware toolkit. Cybercriminals utilise these toolkits to set on arrangement vulnerabilities to distribute malware or engage in other malicious activities, such every bit stealing corporate data, launching denial of service attacks or edifice botnets.
Preventing exploit kits
To guard against exploit kits, an organisation should deploy antimalware software likewise every bit a security plan that continually evaluates if its security controls are effective and provide protection against attacks. Enterprises should also install antiphishing tools considering many exploit kits utilise phishing or compromised websites to penetrate the network.
9. Advanced persistent threat attacks
An advanced persistent threat (APT) is a targeted cyberattack in which an unauthorized intruder penetrates a network and remains undetected for an extended period of time. Rather than causing damage to a organisation or network, the goal of an APT assail is to monitor network activeness and steal information to proceeds access, including exploit kits and malware. Cybercriminals typically use APT attacks to target high-value targets, such as large enterprises and nation-states, stealing information over a long period.
Preventing APT attacks
Detecting anomalies in outbound information may be the best style for organization administrators to determine if their networks accept been targeted.
Indicators of APTs include the post-obit:
- unusual activity on user accounts;
- extensive use of backstairs Trojan equus caballus malware, a method that enables APTs to maintain access;
- odd database activity, such as a sudden increment in database operations involving massive amounts of data; and
- the presence of unusual data files, possibly indicating that data that has been bundled into files to help in the exfiltration process.
To combat this type of information security threat, an arrangement should likewise deploy a software, hardware or cloud firewall to guard against APT attacks. Organizations can too use a web application firewall to discover and prevent attacks coming from web applications past inspecting HTTP traffic.
x. Malvertising
Malvertising is a technique cybercriminals use to inject malicious lawmaking into legitimate online advertising networks and spider web pages. This code typically redirects users to malicious websites or installs malware on their computers or mobile devices. Users' machines may go infected fifty-fifty if they don't click on anything to start the download. Cybercriminals may apply malvertising to deploy a variety of moneymaking malware, including cryptomining scripts, ransomware and banking Trojans.
Some of the websites of well-known companies, including Spotify, The New York Times and the London Stock Commutation, have inadvertently displayed malicious ads, putting users at risk.
Preventing malvertising
To prevent malvertising, advert networks should add validation; this reduces the chances a user could be compromised. Validation could include: Vetting prospective customers past requiring legal business paperwork; two-gene authentication; scanning potential ads for malicious content before publishing an ad; or possibly converting Flash ads to animated gifs or other types of content.
To mitigate malvertising attacks, web hosts should periodically bank check their websites from an unpatched organisation and monitor that system to discover any malicious action. The spider web hosts should disable any malicious ads.
To reduce the take a chance of malvertising attacks, enterprise security teams should be certain to go on software and patches up to appointment as well as install network antimalware tools.
This was last published in March 2021
DOWNLOAD HERE
Posted by: thompsontimstrance1974.blogspot.com
Postar um comentário for "Which Of The Following Scenarios Illustrates A Drive-By Download? UPDATED"